Efficient computation on oblivious RAMs | Proceedings of the twenty-second annual ACM symposium on Theory of Computing

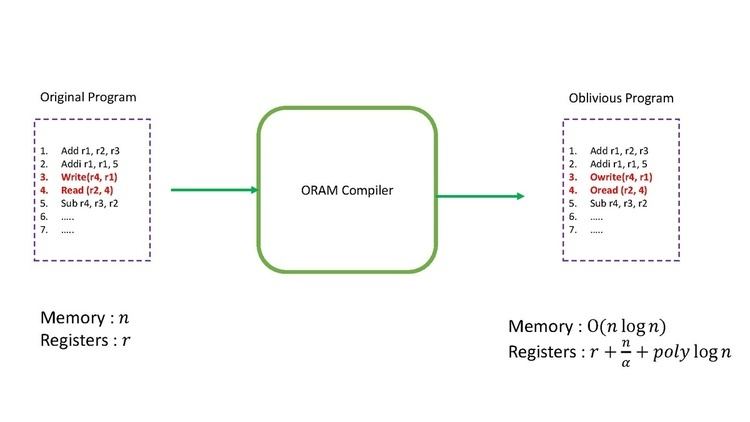
CS7380: Privacy Aware Computing Oblivious RAM 1. Motivation Starting from software protection Prevent from software piracy A valid method is using hardware. - ppt download

CS7380: Privacy Aware Computing Oblivious RAM 1. Motivation Starting from software protection Prevent from software piracy A valid method is using hardware. - ppt download






![PDF] Towards Practical Oblivious RAM | Semantic Scholar PDF] Towards Practical Oblivious RAM | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/b02ac02e19aa1fe2dca6afde5ca6d2d703a8b995/8-Figure4-1.png)